Best Third-Party Risk Management Software [Reviewed for 2024]

Table of Contents
You should take all of the security measures that experts recommend to get your data protection system tight. However, after all of that work, your business can get into trouble because of a slip up at one of your suppliers. Welcome to the hell that is known as “third-party risk.” We will explain what it is and how to reduce it.
Which Companies Are Susceptible to Third-Party Risk?
The frustrating fact about third-party risk is that it can affect any business. Large companies have larger budgets to put extensive risk analysis, vulnerability scanning, intrusion protection systems, and data loss prevention services in place. However, even large multinationals have been caught out by third-party security weaknesses and those providers that caused the problem were themselves of considerable size.
2023 saw headlines about suppliers that had extensive client lists revealed as providing entry points to hackers and data thieves. Progress Software discovered in May 2023 that its MOVEit secure file transfer utility had a security flaw that enables data thieves to gain entry to the systems of its clients. That list of users included the BBC and the government of Nova Scotia, both of which were infiltrated by the Clop hacker group.
More examples of reputable and large suppliers that enabled data thieves to attack their clients include Okta, the identity and access management provider. Its system facilitated hacker access to its client in two waves during 2023, caused by two different security weaknesses. In August 2023, data thieves stole data on 47,000 police officers from the London Metropolitan Police by discovering a security weakness in the software of Digital ID a producer of physical access swipe cards.
Small businesses are more vulnerable to hacker attacks, partly because they are more focused on their core activities, but also because they don’t have the budget for security software or because they don’t understand that all sizes of businesses can be targets. By lack of diligence, an SME can be the target of an attack that could also impact its clients.
What Is Third-Party Risk Management Software?
Third-party risk management software, or vendor risk management, is specialized SaaS tools that identify, analyze, and mitigate external challenges from service providers, IT vendors, contractors, and other third parties.
A third-party, or a vendor, represents a potential risk to your data and should be vetted as such. Why? Because they may have access to your proprietary systems via APIs or certain parts of your database to help them do their jobs. Your suppliers, manufacturers, affiliates, distributors, resellers, partner agencies, or even contractual staff have insider access without the same level of operational oversight as full-time employees.
That's where third-party risk management tools step in. These systems offer tools to assess, rectify, and remediate risk and help organizations guard against institutional and reputational damage.
What's the Difference Between Vendor Risk and Third-Party Risk?
The term is often used interchangeably, and both vendor risk management and third-party risk management can mean the same thing. The only difference we find is:
- Vendors often refer to physical suppliers of raw materials, goods, and other items businesses need on an ongoing basis.
- Third-parties cover both vendors of physical goods as well as other entities that have access to your business, such as contractors, software products, distributors, and more.
Best Third-Party & Vendor Risk Management Software
Let's dive into our list:
1. Enzuzo (Best All-Around Tool)
Enzuzo offers the best all-around option for vendor risk management with plans that deliver the goods without breaking the bank.
The Enterprise plan is customized for mid-market customers and up who require robust third-party risk management oversight. This includes real-time updates on risk levels, streamlined vendor lifecycle management, security questionnaires, and dashboards that give you a 360-degree overview.
Enzuzo Key Features
Key features of Enzuzo's third-party risk management software include the things highlighted above as well as other data privacy management tools such as cookie consent management, data access requests, and privacy workflows designed to keep you compliant with the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA).
Enzuzo's all-in-one platform offers built-in data privacy compliance dashboards tailored to your needs, providing a comprehensive view of risk assessment, data access requests, and consent management. Users can quickly evaluate compliance gaps and monitor third-party data access.
Enzuzo's data privacy co-pilot program addresses compliance, governance, and data mapping challenges. This allows organizations to build sensitive data inventories and custom classifications. The platform also offers incident management and reporting capabilities upon request.
Additionally, Enzuzo provides foolproof privacy impact assessments and a record of processing activities. This enables organizations to understand how internal projects impact personally identifiable information and maintain GDPR compliance. The platform offers best-in-class templates and checklists for monitoring PIAs, compliance with GDPR Article 30, and international data transfer assessments.
Most notably, Enzuzo's vendor management tools empower organizations to share customer data confidently. The platform uncovers reliable vendor prospects, evaluates their privacy protocols, and stays informed about ongoing legal developments and privacy shifts. Users can leverage ready-made templates that conduct vendor evaluations, avoid high-risk vendors, and mitigate the risk of lawsuits and damaging news stories, ensuring a robust, compliant vendor management process.
Competitive Pricing & Contracts
Enzuzo's solutions come with a pricing guarantee — it's called the best all-round solution for a reason. While all enterprise plans are catered to individually, Enzuzo guarantees cost savings compared to other vendors.
The Enzuzo platform is offered in six editions and the first of these is Free. That Free version is great for small websites because it provides a consent banner, DSAR management, and a compliance checklist. However, it doesn’t include third-party risk management. In fact, you need to choose the top plan, called the Enterprise edition, to get that feature.

Custom Workflows & Integrations
Enzuzo works hand in glove with its enterprise partners to develop new workflows unique to their business. Some workflows built for previous clients include the ability to configure cookie banners separately and dynamically. Another workflow was a request to integrate legal policies directly into a website built on an application framework.
Trusted by Global Clients
A recent competitive bidding process saw Enzuzo secure the business of Lucy Group — an international electric business that employs over 1,600 people across 5 continents and 12 countries.
Similarly, Enzuzo powers the data privacy needs of the Power Corporation of Canada, a globally recognized management and holding company specializing in financial services across North America, Europe, and Asia.
Both organizations depend on Enzuzo for critical data privacy support and management — and it can certainly solve similar challenges for businesses looking for the best third-party risk management tools.
🏆 Read how Global Conglomerate Lucy Group chose Enzuzo as its data privacy partner [2023 Case Study]
Positive Reviews on UX, Customer Support, and Onboarding
Feedback from users highlights Enzuzo's commitment to exceptional user experience, responsive customer support, and streamlined onboarding processes. Clients appreciate the platform's intuitive design, the efficiency of customer support teams, and the comprehensive onboarding resources. These all facilitate a smooth transition and ongoing engagement with Enzuzo's solutions.
Get a complimentary 1-1 strategy call to understand your requirements. Book a time here👇
2. OneTrust (Best for Fortune 500s)
OneTrust is an enterprise-level vendor management solution that’s earned a spot among the leading risk management platforms. Founded in 2016, readers are familiar with OneTrust’s resume as an intelligence solution. The platform's comprehensive suite offers functionalities that range from robust privacy management to meticulous vendor risk assessments. This positions it as a frontrunner for businesses with compliance targets.
However, OneTrust comes with significant costs. It’s hard to overlook its substantial price tag; for many organizations, especially smaller entities with limited budgets, the licensing fees, implementation costs, and ongoing expenses may be prohibitive.
The OneTrust platform includes an automated workflow for third-party risk assessments. The data sought by this process will adapt to the specific data privacy standard that you select in the settings for the entire service. The service gathers data about each associated business and seeks clarification from the external company through questionnaires. The process keeps a general scan running throughout the service life of the OneTrust platform and will rerun its full risk assessment process if news about that partner appears.
For larger companies, however, OneTrust is a clear standout in terms of performance. Its advanced features make it our top choice for enterprises and Fortune 1000s that need a comprehensive service for trust intelligence. It’s worth noting, however, that OneTrust scores relatively low in customer service. Many customers report difficulty getting problems resolved.
Other than OneTrust’s high costs, users must commit to long-term contracts. While we stand behind OneTrust as a top choice, companies must weigh these costs against its benefits.
3. SecurityScorecard
SecurityScorecard is another solution that brings visibility and control to a company’s security posture. As an enterprise-level solution on the same tier as OneTrust, SecurityScorecard brings many of the same benefits—and drawbacks—to the table.
Users love SecurityScorcard’s advanced feature set that goes beyond security postures to attack surface management, threat intelligence, and risk quantification. SecurityScorecard offers an automatic vendor detection tool that streamlines processes in some interesting ways. The platform helps users visualize third- and fourth-party risk levels, detects all vendors in the ecosystem, and continuously monitors supply-chain risk.
On the flip side, SecurityScorecard is expensive, and its functions come with a steep learning curve. Like many vendor management solutions at this level, onboarding difficulty is a concern, particularly given the platform’s high costs. (While a free option is available, most businesses will feel limited by basic functionality.)
Users can expect to invest substantial time in onboarding after purchase, although the time spent on training may be worthwhile when the platform’s full features are considered. And users report high marks for SecurityScorecard’s customer service, so any needed support should be readily available.
SecurityScorecard offers a managed service for businesses that don’t have cybersecurity teams to manage vulnerabilities and third-party risk assessments. The SOC team of SecurityScorecard will perform a full supply chain risk assessment. The service notifies you of a supplier risk and, to be fair, also informs that business of the problem. That notification includes a description of the problem and suggestions on how to resolve it. The service continues to monitor all businesses in the supply chain for newly arising security failures.
4. Aravo
Aravo offers a comprehensive approach to third-party risk management software. At its core, Aravo centralizes third-party relationships by integrating various risk domains throughout the entire lifecycle of a relationship. This gives users a single, auditable inventory spanning from initial nomination to offboarding. Its centralized approach ensures both transparency and traceability.
One of the notable features of the Aravo platform is its configurability. With pre-configured workflows and AI-driven capabilities, the platform expedites critical processes for more seamless operations. Aravo's adaptability allows users to modify solutions as requirements evolve swiftly. This keeps the platform aligned with an organization's changing needs.
For organizations that want a deeper dive into risk evaluations, Aravo provides enhanced due-diligence applications. These industry-aligned workflows and machine-learning support allow organizations to align their risk assessments with regulatory guidelines.
Regarding scalability, Aravo’s flexibility caters to a broad spectrum of organizational needs. Whether an organization seeks a basic system to automate manual tasks or requires a comprehensive solution to manage an expansive third-party network, Aravo can adapt accordingly.
However, while Aravo presents robust functionalities, the platform may not be for everyone. Aravo comes with the high costs expected of an enterprise vendor management solution. Companies should contact the company directly for exact quotes. Some users have reported occasional performance issues with Aravo and inconveniences with usability. While Aravo brings an impressive suite of features to the table, these drawbacks should be weighed before purchase.
5. Panorays
Panorays offers helpful features across security assessments, monitoring, vendor engagement, and security programming. Panorays gives organizations a deep dive into their risk landscape through comprehensive evaluation tools. These tools provide a more nuanced understanding of each vendor’s cybersecurity posture.
Panorays streamlines vendor assessment with its specialized, customizable tools that increase efficiency. The platform provides pre-built templates for security questionnaires that ensure consistent evaluations of vendor cybersecurity postures. Organizations benefit from customizable remediation plans and tailored strategies to address specific vulnerabilities or operational nuances.
Panorays' reporting capabilities offer actionable insights through out-of-the-box reporting. These simplify complex data into understandable metrics for better decision-making. Additionally, the platform emphasizes proactive security with external surface assessments and ongoing monitoring. This is an essential way for organizations to identify and address risks promptly.
Regarding drawbacks, Panorays lacks in some self-service areas and has limited integration potential with other systems. For some companies, this may make Panorays a non-starter. However, the platform offers a series of helpful pricing tiers based on how many continuous vendor assessments the business wants to achieve.
6. Resolver
Resolver’s comprehensive third-party risk management software enhances vendor management throughout the partnership lifecycle. The platform optimizes vendor selection, efficient onboarding, and streamlined compliance management in numerous ways.
Key features include simplified vendor onboarding through customizable questionnaires and a multilingual solution. A vendor portal complements these and centralized documentation for enhanced collaboration. Resolver's platform brings transparency to monitoring and risk assessments, which provide notifications on changes to vendor risk profiles. It also supports automated workflows for consistent risk management.
Additionally, Resolver’s vendor management solutions promote collaboration and compliance by allowing vendors to input data, complete assessments, and access vital documents, all of which foster mutual understanding. There are handy tools for information security and risk leaders. Additional tools promote third-party insights that allow stakeholders to strengthen assessments, allocate resources effectively, foster enhanced partnerships, and maintain compliance.
Enterprises of all sizes use Resolver, though the company lacks transparency in its service plans and tiers. Companies must contact the company directly to request a demo or discuss pricing options, which can be frustrating. If Resolver’s features suit the company’s needs, some research may be justified—though users will need to do more legwork with Resolver than with some other options on this list.
7. Vanta
Vanta is another great choice to automate compliance and streamline security reviews. Aside from its broad range of compliance and security features, the platform’s dedicated tools build transparency across the business—including with third-party vendors. Vanta’s third-party risk management software includes tools that automate vendor discovery, risk assessments, and remediations. These help companies spend less time on security reviews and more time on core business goals.
Regarding its target market, Vanta caters to a wide range of businesses, from startups to large enterprises, across various industries. While the platform is scalable and customizable to meet different organizations’ needs, it’s best suited for mid-sized companies that need assistance to navigate complex compliance landscapes.
Vanta offers three pricing tiers: Core, Collaborate, and Scale. Prices aren’t available online, so prospective purchasers must contact Vanta directly for quotes. While many users report good experiences with Vanta, some mention challenges with onboarding and some communication breakdowns with Vanta’s support teams. While Vanta is an excellent choice for trust management, especially for mid-size companies, its implementation processes may be a challenge.
8. Ketch
Ketch has emerged as a significant player in third-party risk management software. It offers a comprehensive platform for vendor assessment, risk mitigation, and compliance automation. Unlike traditional third-party risk management solutions, Ketch’s platform seamlessly integrates applications, infrastructure, and APIs. These streamline third-party risk evaluations and enhance compliance procedures.
Ketch offers another great set of features to help transform third-party risk management. With its advanced risk assessment tools and AI-powered analytics, Ketch is ideal for vendor evaluation, risk scoring, compliance monitoring, and more. Users commend Ketch's support team and its adaptability as third-party risk management software.
However, Ketch's limitations involve a substantial price tag and some significant technical complexities. The company imposes lengthy contractual commitments on its customers, which require upfront, long-term engagement. Prospective users should evaluate whether Ketch's feature set justifies the investment, although those who do commit will enjoy Ketch’s innovative approach to risk management.
Ketch’s user base appreciates the platform’s robust features, scalability, and dependable customer support. However, as with other comprehensive third-party risk management platforms, users encounter trade-offs in terms of high costs and extended contract durations. We can recommend Ketch as a viable alternative to traditional third-party risk management solutions, although users who seek a more specialized or cost-effective option may find better alternatives elsewhere.
9. UpGuard
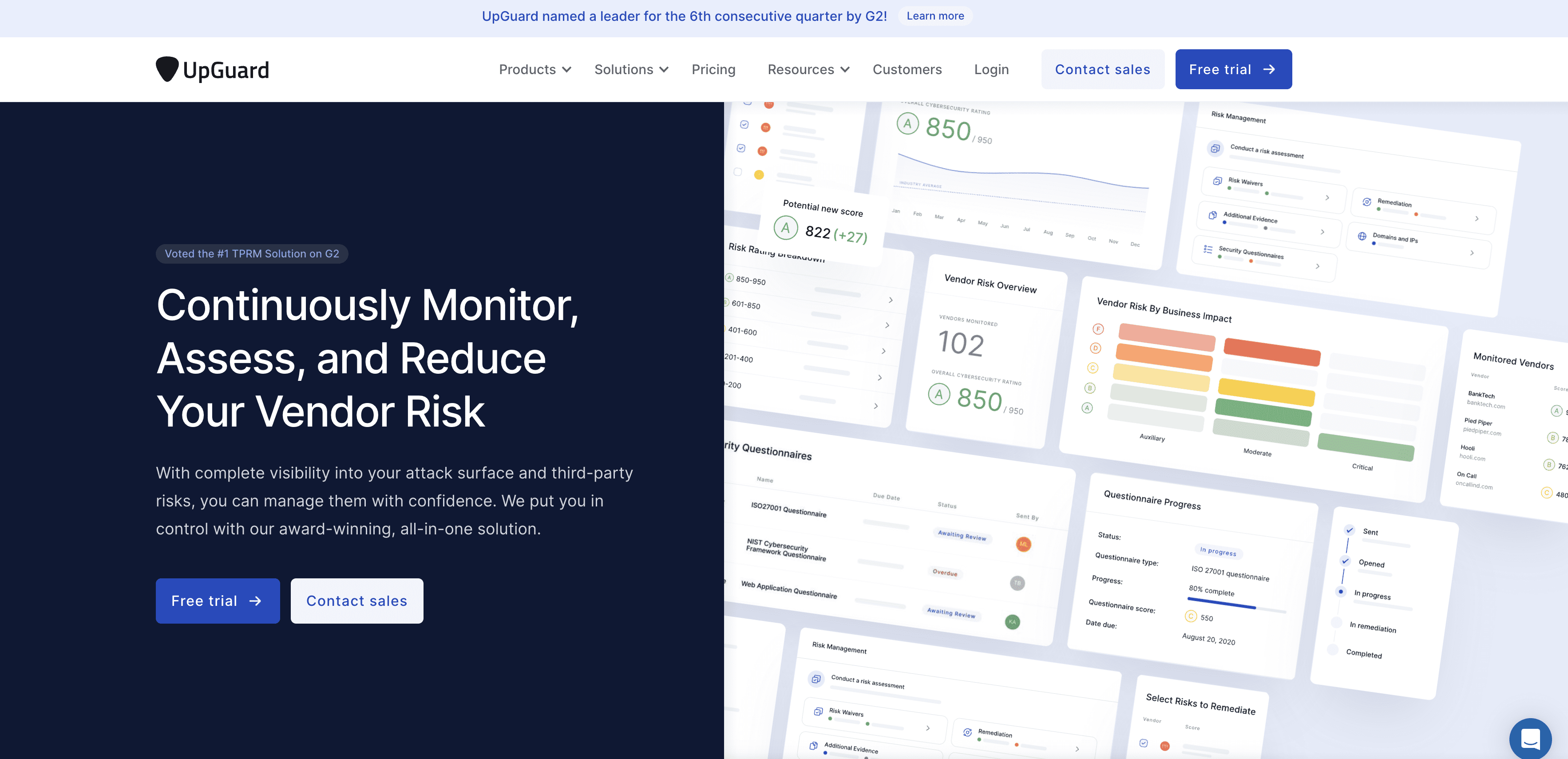
UpGuard has developed a strong following with an emphasis on security-rating mechanisms, vendor risk evaluations, cybersecurity posture analyses, and continuous surveillance. These vendor management solutions empower both large enterprises and mid-sized businesses to establish robust security frameworks that reduce vendor risk.
A standout feature of UpGuard is its ability to mitigate cyber risks, enhance security postures, and adhere to diverse industry regulations and standards. While the platform does encompass compliance management tools, its primary focus is to evaluate and mitigate risks associated with vendors and third-party entities.
UpGuard's Vendor Risk tool furnishes a unified dashboard dedicated to third-party risk evaluations that facilitate streamlined risk assessment processes, vendor interactions, and real-time updates on security stances. The UpGuard BreachSight tool addresses critical security concerns to manage their external threat landscapes, enable organizations to promptly identify and counteract emerging security vulnerabilities, and preserve hard-earned customer trust.
Note that UpGuard's vendor risk management software extends beyond these highlighted tools. It encompasses a wide array of solutions that span the entire security remediation lifecycle—from monitoring and analysis to actionable insights and ongoing management. This holistic approach has solidified UpGuard's reputation as a trusted provider in the realm of risk assessment solutions.
However, its drawbacks include a suboptimal user experience across tools that pose usability challenges and high costs that may present financial hurdles for smaller enterprises. Pricing is tiered and ranges from $19,000/year to $90,000/year for listed plans. Custom pricing plans are available for enterprises, although each business should do its due diligence before it commits to any long-term plans.
What are the Benefits of Third-Party Risk Management Software?
It's next to impossible to run a business without having partnerships with external stakeholders — whether that's contractors, distributors, software providers, or marketing partners. This adds to the complexity of your cybersecurity mix — and where third-party software helps.
Reduced Threat of Data Breaches
The big problem with third-party risk is that there is nothing you can do about it other than predict it and avoid it. So, third-party risk management aims to reduce the possibility of a data breach being caused by the lax security of a provider.
An example of a third party that can cause data breaches from your company to occur would be a cloud storage service that has insufficient access protection. That service’s shortcomings would allow hackers to steal the data that you store there. In this case, it would be nice to say that the insufficiencies of the third party are not your fault. However, legally, you would be held accountable for that data breach.
Another example of a third-party risk would be an identity and access management service, such as an SSO network. If a hacker can trick that, every company that uses that service can be accessed. In this case, the data breach would be a theft from your storage but caused by a weakness in the third party.
In both cases, your company must protect the data that has been entrusted to it and the fines and reputation damage will fall on it even if the fault occurred in a third-party business. Thus, you need to assess those associated businesses and refuse to deal with them if they don’t meet a suitable security standard.
Regulatory Compliance Management
Data privacy laws like GDPR, CCPA, LGPD, and PIPEDA mandate that organizations monitor sensitive data shared with third parties and conduct privacy impact assessments when transferring data.
There are mechanisms to spread the legal responsibility for attacks that alter, delete, or steal data. For example, the HIPAA rules about protected health information (PHI) allow for a data holder to spread the responsibility with a third party, such as a storage provider, by creating a business associate agreement (BAA). This contract would reduce the third-party risk that could impact your company because it would state how the supplier should contribute to any fines that a breach would incur.
Although the concept of a BAA isn’t built into other data protection standards. There is nothing to stop you from constructing your own agreement. That could offload the consequences of failure by the third party onto that other company. So, it is possible to make a third party take financial responsibility for any potential failure and that would be a very effective way to reduce third-party risk. However, under that scenario, you would still need a form of third-party risk assessment to ensure that the company had sufficient funds available to meet any fines that you could face for their errors, or that they have sufficient cover from professional insurance.
Choosing the right software can help with these tasks.
Costs and Operational Overheads
With the average cost of a data breach nearly $5 million, it's safe to say that the risks of not investing in third-party software are too great to ignore. These apps will give you knowledge and visibilty into the safety of your external partners, helping you secure your systems and address operational deficiencies.
How to Pick the Right Vendor Risk Management Software
One must go beyond surface-level assessments to evaluate potential vendor management solutions; be sure to delve into their features, target market, and scalability potential to assure alignment with each organization's risk management criteria. At the minimum, a risk management platform should provide insights into the following key areas:
- Policies: Assess the policies and industry standards suppliers adhere to; gauge their capability to meet basic risk management criteria expected of them.
- People & Training: Evaluate the expertise and training of vendors' staff to make sure they can support your operations without posing inherent risks.
- Operating Analysis: Analyze the safety and integrity of your third-party partners' internal operations, systems, and processes to determine the level of risk they may introduce to your organization.
- Pricing: Weigh costs and functionalities of third-party risk management software. Inquire about pricing, trial availability, discounts, and flexible payment plans.
- Data Reliability: Make sure the platform sources data from reputable entities and regularly updates its sources. Data quality is paramount in risk management tools. Evaluate the platform's integration capabilities with your existing systems to maintain reliable risk assessments.
- Assessment Timeline: Assess the platform's typical assessment duration, training requirements, and availability of ongoing support. Consider automation features that allow continuous operation and comprehensive reporting capabilities for monitoring progress.
- User-Friendliness: Evaluate the platform's user interface, available guides or manuals, integration capabilities, customization options, and documentation requirements for a seamless and intuitive user experience. Usability plays a key role in platform effectiveness.
Learn more about how Enzuzo can assist with your third-party risk management needs. Book 1-1 time with Mate Prgin, CEO👇

Osman Husain
Osman is the content lead at Enzuzo. He has a background in data privacy management via a two-year role at ExpressVPN and extensive freelance work with cybersecurity and blockchain companies. Osman also holds an MBA from the Toronto Metropolitan University.